GQSCD-Core defines how hardware, firmware, operating system, and
application components on an end-user device can provide verifiable
signature-creation properties aligned to qualified-signature security
objectives ([EU-910/2014],
[EU-2016/650]).
This specification is technical and does not itself grant legal
qualification ([EU-910/2014],
[EU-TRUSTED-LISTS]).
This is an unofficial draft.
AI assistance disclosure: this draft used OpenAI GPT-5 Codex for
drafting support, structure proposals, and editorial rewrites. Human
editor review determined normative content, accepted/rejected changes,
and final wording.
Source currency note: linked source pages were checked on February 17,
2026 and February 18, 2026.
Scope
This specification covers:
-
Defines a component security profile for end-user signing devices ([EU-910/2014], [EU-2016/650]). EU qualification
mappings in this specification target [=qualified signature creation
device=] outcomes.
-
Defines outcome invariants and verifier behavior, while leaving
implementation architecture and optimization choices to implementers.
-
Defines explicit threat assumptions and non-trust assumptions ([ETSI-319401]).
-
Defines a primary Web Profile and an EU Compatibility Profile ([WEBCRYPTO-L2], [WEBAUTHN-L3],
[EU-2024/2982]).
-
Defines a mapping from GQSCD properties to eIDAS Annex II style
objectives ([EU-910/2014],
[EU-2016/650]).
Normative Interface Surface
This specification defines invariants, processing rules, and conformance
semantics. Contract details in openapi.yaml
are draft interface artifacts and this document does not restate
field-level wire details.
NOTE: The openapi.yaml contracts are
indicative and are not yet normative. Official schemas will be finalized
after the first reference implementation.
Terminology
- end-user device
-
A phone, tablet, laptop, desktop, or hardware authenticator operated
by a natural person in signature workflows.
- signature creation data
-
Data uniquely used by the signatory to create an electronic signature;
aligned with eIDAS terminology for electronic signature creation data
([EU-910/2014]).
- signature creation key
-
Cryptographic private key material used as [=signature creation data=]
in digital signature mechanisms ([RFC7515],
[RFC9052]).
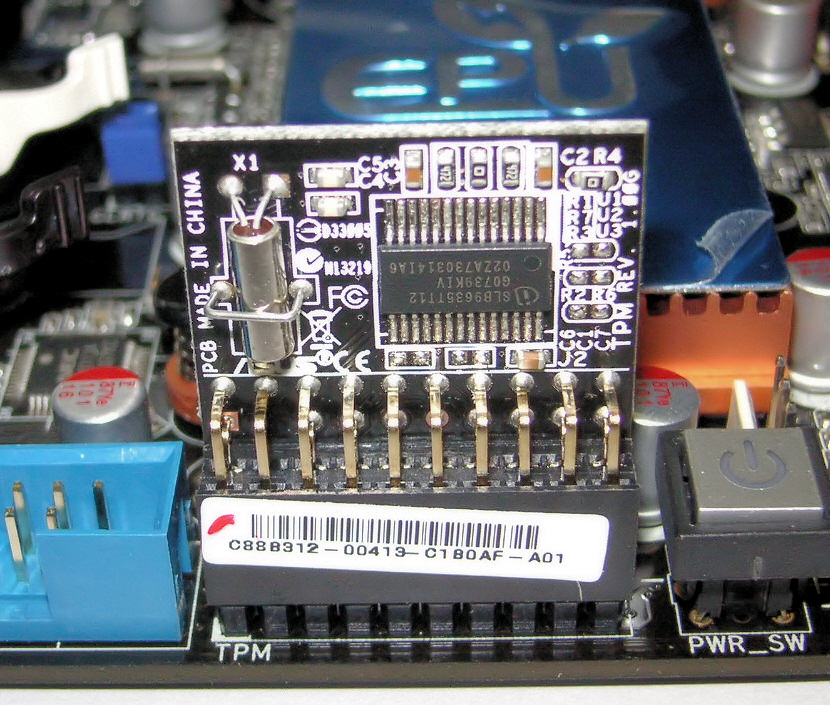
- hardware-backed key
-
A [=signature creation key=] whose generation, storage, and
cryptographic use are enforced by protected hardware boundaries with
non-exportability controls ([ANDROID-KEYSTORE], [MSFT-TPM],
[APPLE-SE]).
- qualified signature creation device (QSCD)
-
Device class defined by eIDAS and evaluated against Annex II outcomes
and referenced assessment standards ([EU-910/2014], [EU-2016/650]).
- sole control
-
Security objective that signature creation data can be used only under
control of the legitimate signatory, as required by Annex II outcome
language ([EU-910/2014]).
- user intent ceremony
-
Complete interaction in which the signer can inspect what is being
signed and explicitly authorize the operation, with security-critical
portions mediated by trusted platform paths when available ([ANDROID-PROTECTED-CONFIRMATION], [WEBAUTHN-L3]).
- user approved object
-
The exact full payload byte sequence presented to and approved by the
signer before signature creation; this profile does not permit signing
operations where only a partial or transformed subset is shown as the
approval target ([EU-ANNEX-II],
[ANDROID-PROTECTED-CONFIRMATION], [RFC7515],
[RFC9052]).
- proof object
-
JSON object attached to an artifact that carries cryptographic proof
metadata and proof bytes so a verifier can check integrity and
authenticity deterministically ([VC-DI]).
-
DataIntegrityProof
-
[=proof object=] type defined by the W3C Data Integrity model; in this
profile it is used for profile-level integrity claims and is paired
with the selected
cryptosuite and
proofValue members ([VC-DI], [VC-DI-ECDSA]).
- zero-trust verification model
-
Verification model where each decision is based on explicit
per-transaction evidence and policy evaluation, rather than implicit
trust in network location, client software, or governance labels alone
([NIST-SP-800-207],
[RFC7515],
[RFC9052]).
- trusted computing base
-
Set of hardware, firmware, and software components that must behave
correctly to uphold stated security properties ([ETSI-319401]).
- evidence record
-
Machine-verifiable artifact set used to substantiate technical or
legal property claims ([ETSI-319401],
[EU-2016/650]).
- gqtsp discovery endpoint
-
Deployment-defined HTTPS discovery location used to publish evidence
metadata and pointers for decentralized verifier retrieval in this
profile ([RFC8615],
[RFC9110],
[GDIS-CORE],
REQ-GDIS-05,
getSchemeDescriptor,
getEndpointKindCatalog,
getEventLogView, and
getEventHeadMeta).
- local signing profile
-
Model where signature creation data remains on the signatory-operated
[=end-user device=] and is not duplicated to remote service custody.
- remote signing model
-
Model where signature creation data is created, managed, or activated
in server-side trust-service components external to the signatory
device ([CEN-419241-1],
[ETSI-119431-1],
[ETSI-119431-2]).
- web profile
-
Primary interoperability profile in this specification, based on
globally deployed web and internet standards ([WEBCRYPTO-L2], [WEBAUTHN-L3],
[RFC7515],
[RFC9052]).
-
eu compatibility profile
-
Mapping layer from [=web profile=] artifacts to EU legal and ecosystem
evidence requirements ([EU-910/2014],
[EU-2016/650],
[EU-2024/2979],
[EU-2024/2982]).
- qualified status claim
-
Claim that an actor, service, device, or signature has legal qualified
status within a defined jurisdiction; such claims require
authoritative status evidence ([EU-TRUSTED-LISTS], [EU-QSCD-NOTIFICATIONS]).
- eidas framework
-
EU legal framework for electronic identification and trust services
established by Regulation (EU) No 910/2014 and its amendments ([EU-910/2014], [EU-2024/1183]).
Architecture and Data Model
REQ-GQSCD-01: Unless explicitly overridden in this
specification, data-model terms such as list, set, tuple, byte sequence,
and algorithm-step vocabulary MUST follow WHATWG Infra ([WHATWG-INFRA]).
REQ-GQSCD-02: JSON values used for evidence payloads
and discovery metadata MUST conform to RFC 8259, and canonical JSON
bytes used by this profile for digest inputs MUST use RFC 8785 JCS ([RFC8259], [RFC8785]).
REQ-GQSCD-03: If controller documents are used for key
and service endpoint discovery, they MUST conform to Controlled
Identifiers v1.0 semantics and processing rules ([CONTROLLER-DOCUMENT]).
REQ-GQSCD-04: [=proof object=] instances used for
profile-level integrity claims MUST use the Data Integrity model (type: [=DataIntegrityProof=]) with a cryptosuite defined by [VC-DI-ECDSA], and MUST include
cryptosuite and proofValue members ([VC-DI], [VC-DI-ECDSA]).
The machine-readable schema bindings for these proof structures are
defined in openapi.yaml#/components/schemas/ProofObject and
openapi.yaml#/components/schemas/DataIntegrityProof.
REQ-GQSCD-05: Payload digests and evidence digest
values defined by this profile MUST use sha-256, and digest
bytes MUST be serialized as base64url without padding ([RFC8785], [BASE64URL]).
Deterministic Verification Algorithm
REQ-GQSCD-06: Verifiers MUST execute the following
deterministic algorithm for each evidence artifact:
-
Parse the artifact as JSON and fail with
ERR-GQSCD-MALFORMED-JSON if RFC 8259 validation fails.
-
Validate required profile fields and fail with
ERR-GQSCD-SCHEMA if required members are absent.
-
Verify the Data Integrity proof using the transformation,
canonicalization, hashing, proof serialization, and proof
verification algorithm defined by the artifact's
cryptosuite and fail with
ERR-GQSCD-PROOF on failure.
-
Canonicalize the application payload bytes using RFC 8785 JCS,
compute
sha-256, and compare against the declared
user-approved-object digest; fail with
ERR-GQSCD-PAYLOAD-DIGEST on mismatch.
-
Verify freshness windows (
issuedAt,
expiresAt, and profile status metadata) and fail with
ERR-GQSCD-FRESHNESS if stale or not yet valid.
-
Emit deterministic pass/fail output containing the failing code set
and matching requirement identifiers aligned with
GQTS failure semantics.
Cryptographic suite transitions and verifier compatibility policy
SHOULD remain aligned with
REQ-GDIS-07.
Threat Model
REQ-GQSCD-08: Implementations MUST model attacker
capabilities including network control, malicious local process
execution, UI overlay/tapjacking, software rollback attempts, and
dishonest relying-party behavior ([ETSI-319401],
[ANDROID-PROTECTED-CONFIRMATION]).
REQ-GQSCD-09: A conformance report MUST explicitly list
the [=trusted computing base=], trust assumptions, and excluded trust
assumptions ([ETSI-319401]).
REQ-GQSCD-10: Implementations MUST NOT treat UI labels,
software allowlists, or relying-party declarations as sufficient
security evidence without cryptographic verification ([EU-910/2014], [RFC7515],
[RFC9052]).
REQ-GQSCD-11: GQSCD-Core Class A conformance targets a
[=local signing profile=]: [=signature creation data=] MUST remain
inside signer-controlled hardware-backed boundaries, MUST NOT be
exported as raw key bytes, and MUST NOT be duplicated for backup or
escrow in this profile ([EU-ANNEX-II],
[EU-2016/650]).
| Threat |
Required mitigation |
Reference basis |
| T-01 key exfiltration |
Use [=hardware-backed key=] custody and deny raw private-key
export.
|
[ANDROID-KEYSTORE],
[MSFT-TPM],
[WEBAUTHN-L3]
|
| T-02 UI deception |
Bind [=user intent ceremony=] to exact payload digest and policy.
|
[ANDROID-PROTECTED-CONFIRMATION], [WEBAUTHN-L3],
[APPLE-SECACCESSCONTROL]
|
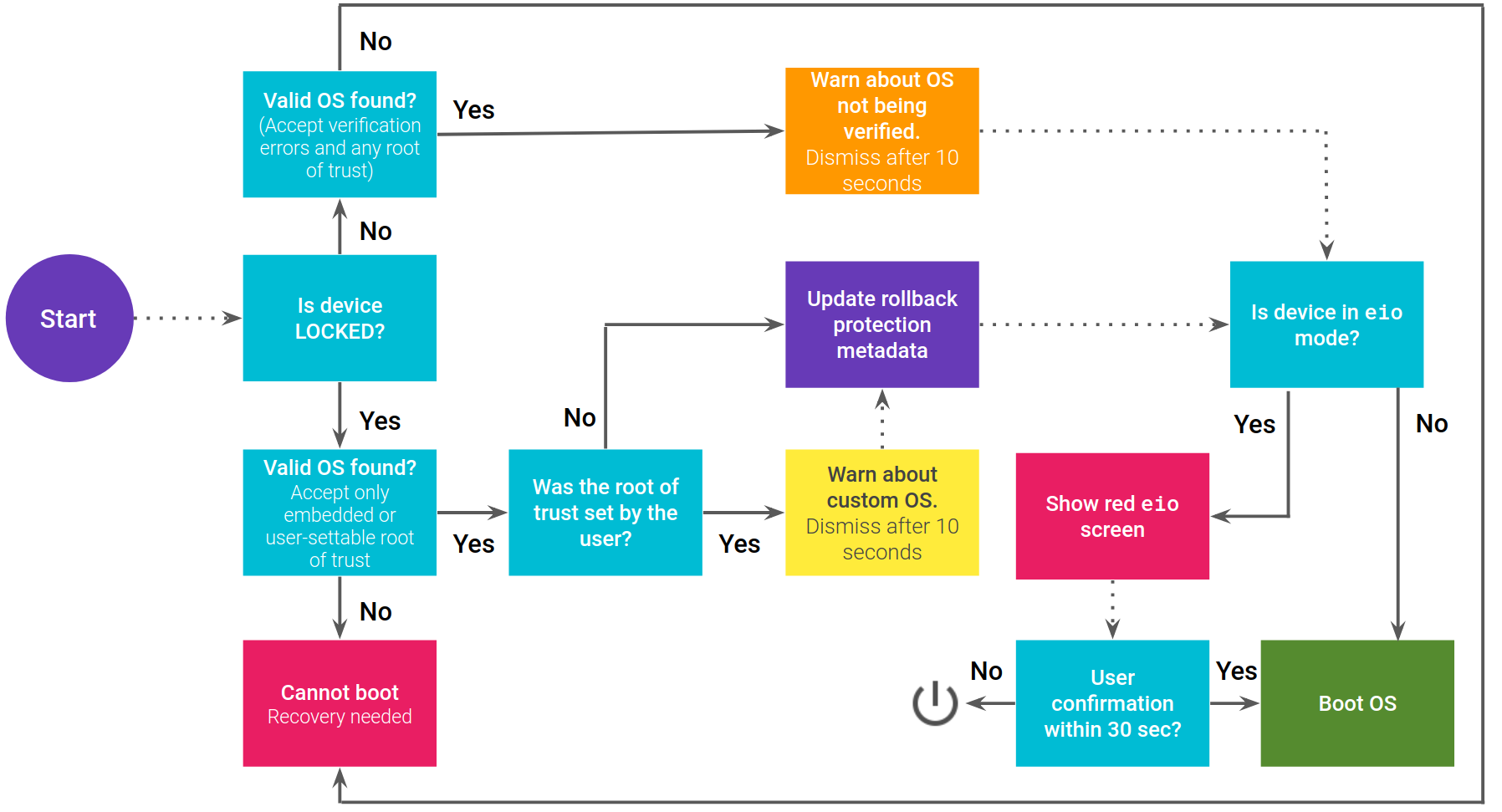
| T-03 rollback |
Use anti-rollback with signed update provenance. |
[ANDROID-AVB],
[ANDROID-KEYMINT-VERSION-BINDING], [MSFT-SECURE-BOOT],
[APPLE-LOCALPOLICY]
|
| T-04 registry spoofing |
Validate signed, freshness-checked [=evidence record=] artifacts.
|
[EU-TRUSTED-LISTS],
[EU-QSCD-NOTIFICATIONS],
[RFC7515],
[RFC9052]
|
| T-05 remote key mediation misuse |
Keep key custody local to the signatory device; treat [=remote
signing model=] as out-of-scope for GQSCD-Core Class A.
|
[EU-ANNEX-II],
[ETSI-119431-1],
[ETSI-119431-2],
[ETSI-119432]
|
Normative Requirements
-
REQ-GQSCD-12:
Implementations MUST generate and use [=signature creation data=]
inside hardware-backed boundaries and MUST prevent private-key export
in raw form ([=ANNEXII-1a=], [=ANNEXII-1c=], [=ANNEXII-1d=]).
-
REQ-GQSCD-13:
Implementations MUST NOT support private-key backup, escrow, or
duplication in GQSCD-Core Class A profiles ([=ANNEXII-1a=],
[=ANNEXII-1d=]).
-
REQ-GQSCD-14:
Each signature operation MUST be bound to one [=user approved object=]
and that object MUST be the complete payload intended for signature
([=ANNEXII-2=]).
-
REQ-GQSCD-15:
Implementations MUST produce machine-verifiable evidence artifacts for
key custody, user-approval binding, and platform state assertions
([=ANNEXII-1a=], [=ANNEXII-1d=], [=ANNEXII-2=]).
-
REQ-GQSCD-16: The [=remote signing model=] is
NOT RECOMMENDED as baseline behavior in this
core profile and is out-of-scope for Class A conformance; ecosystems
choosing that model MUST specify a separate threat model and assurance
profile ([ETSI-119431-1],
[ETSI-119431-2],
[ETSI-119432]).
Evidence Model
REQ-GQSCD-17: Conforming implementations MUST emit
[=evidence record=] artifacts that are independently verifiable by third
parties and bound to explicit Annex II clause IDs.
In this profile, wallet-held proof artifacts (for example identity
binding credentials and signing-event credentials) are private claims by
default and are not published to GQTS hosts; only public verification
material and discovery metadata are published on the trust network.
Published material is treated as self-certifying only after
cryptographic verification and policy evaluation by a verifier.
Evidence Artifact Profile
-
REQ-GQSCD-18:
Evidence proof artifacts MUST be represented as integrity-protected
verifiable credentials and MUST include issuer, subject key
identifier, issuance time, expiration/status, and proof material.
These proof artifacts MUST be treated as wallet-private claims
unless explicitly disclosed in verifier presentation flows ([VC-DM2], [VC-DI],
GDIS binding credential).
-
REQ-GQSCD-19:
Each signing event evidence artifact MUST carry a digest of the
[=user approved object=] and a digest or identifier of the produced
signature object so verifiers can check one-to-one binding ([RFC7515], [RFC9052]).
-
REQ-GQSCD-20:
Evidence artifacts MUST include explicit claims for key
non-exportability and MUST declare that private-key backup and
duplication are not supported by the profile instance
([=ANNEXII-1a=], [=ANNEXII-1d=]).
-
REQ-GQSCD-21:
Evidence artifacts MUST include a clause mapping array referencing
one or more of [=ANNEXII-1a=], [=ANNEXII-1b=], [=ANNEXII-1c=],
[=ANNEXII-1d=], and [=ANNEXII-2=] for each asserted security
property.
Decentralized Publication and Discovery
This discovery profile is aligned with the host and governance
publication model used in GDIS and the host-profile operation
invariants defined by GQTS. This section defines only verification
invariants and trust-boundary behavior ([GDIS-CORE],
REQ-GDIS-05,
REQ-GQTS-01
through
REQ-GQTS-07).
Discovery and event-log retrieval in this profile are scoped to public
verification material (for example key references, controller
documents, status pointers, and event-link metadata). Wallet-private
proof artifacts are out of scope for trust-service publication in this
specification ([GQTS-CORE],
GQTS history invariants).
-
REQ-GQSCD-22: Deployments that expose [=gqtsp
discovery endpoint=] metadata for public verification material MUST
do so via HTTPS with deterministic, machine-verifiable content ([RFC8615], [RFC9110],
getSchemeDescriptor,
getEndpointKindCatalog).
-
REQ-GQSCD-23:
Deployments SHOULD align
gidas discovery suffix usage
with the IANA Well-Known URI registry process to reduce namespace
collision risk ([IANA-WELL-KNOWN-URIS], [RFC8615]).
-
REQ-GQSCD-24:
Any operator MAY host a conformant discovery endpoint; host
participation does not grant implicit trust and verifiers MUST
validate signatures, issuer bindings, and freshness on every
retrieved public verification artifact. Wallet-private proof
artifacts remain outside host publication scope ([GDIS-CORE],
REQ-GDIS-09,
REQ-GQTS-03,
REQ-GQTS-05, and
REQ-GQTS-07, [RFC7515],
[RFC9052]).
-
REQ-GQSCD-25:
Implementations SHOULD support replicated host retrieval so
verifiers can detect missing or divergent state views in adversarial
network conditions ([GDIS-CORE],
REQ-GQTS-04,
REQ-GQTS-05, [NIST-SP-800-207]).
Verifier Checklist Profile
-
REQ-GQSCD-26:
Verify integrity and signature validity of each evidence credential
before policy evaluation ([VC-DI], [RFC7515],
[RFC9052],
REQ-GDIS-09).
-
REQ-GQSCD-27:
Verify that evidence for each signature operation links to exactly
one [=user approved object=] and that the digest matches the full
payload bytes presented for signature ([=ANNEXII-2=]).
-
REQ-GQSCD-28:
Verify policy flags asserting non-exportable key usage and reject
any profile state claiming key backup, escrow, duplication, or raw
key export support ([=ANNEXII-1a=], [=ANNEXII-1d=]).
-
REQ-GQSCD-29:
Verify discovery metadata from [=gqtsp discovery endpoint=] and
governance references, then evaluate freshness windows and conflict
handling deterministically. Implementations MUST reject or
explicitly report entries that fail required chain-link or proof
verification checks and MUST NOT silently merge invalid nodes ([GDIS-CORE],
REQ-GDIS-09,
REQ-GQTS-04,
REQ-GQTS-05,
REQ-GQTS-07,
GQTS failure semantics, [RFC8615]).
Interoperability Profiles
Web Profile (Primary)
The primary web profile baseline aligns with
GDIS Web Profile (Primary).
-
REQ-GQSCD-30: MUST be the baseline profile for
interoperability ([WEBCRYPTO-L2],
[WEBAUTHN-L3]).
-
REQ-GQSCD-31: MUST support JOSE/JWS/JWK or
COSE/CBOR signature containers ([RFC7515], [RFC7517],
[RFC9052],
[RFC8949]).
-
REQ-GQSCD-32: MUST support VC-based evidence
records for verifier exchange and archival checks ([VC-DM2], [VC-DI]).
-
REQ-GQSCD-33: SHOULD support WebAuthn for hardware
authenticator mediation where applicable ([WEBAUTHN-L3]).
-
REQ-GQSCD-34: MAY use DID Core, VC Data Model, Data
Integrity, OpenID4VP, and SD-JWT VC when credentials are needed and
deployment maturity requirements are satisfied ([DID-CORE], [VC-DM2],
[VC-DI],
[OPENID4VP],
[SD-JWT-VC]).
-
REQ-GQSCD-35: MUST define security properties in
physical reality terms: key custody, tamper resistance, and
verifiable user intent ([EU-910/2014],
[EU-2016/650]).
Mapping to eIDAS Annex II Style Objectives
For auditability, this section defines explicit clause-level IDs aligned
to Annex II requirement units in eIDAS.
REQ-GQSCD-41: Any normative requirement in this
specification that claims Annex II alignment MUST reference one or more
clause IDs from this section.
| Clause ID |
Annex II requirement unit (condensed) |
Legal source |
| ANNEXII-1a |
Confidentiality of signature creation data is reasonably assured.
|
[EU-ANNEX-II] |
| ANNEXII-1b |
Signature creation data can practically occur only once. |
[EU-ANNEX-II] |
| ANNEXII-1c |
Signature creation data cannot be derived with reasonable
assurance; signature is protected against forgery.
|
[EU-ANNEX-II] |
| ANNEXII-1d |
Signature creation data is reliably protected by the legitimate
signatory against use by others.
|
[EU-ANNEX-II] |
| ANNEXII-2 |
Qualified signature creation devices do not alter data to be
signed and do not prevent prior presentation to the signatory.
|
[EU-ANNEX-II] |
| Annex II clause ID |
EU objective |
GQSCD property |
Evidence |
Remaining delta |
Reference basis |
| ANNEXII-1a |
Confidentiality of signature creation data |
Non-exportable [=hardware-backed key=] with confidentiality
controls
|
Attestation + key policy + lifecycle log |
Formal certification decision process |
[EU-ANNEX-II],
[CEN-419241-1],
[CEN-419221-5]
|
| ANNEXII-1b |
Practical uniqueness of signature creation data |
Controlled key generation with approved entropy source and
uniqueness constraints
|
Key generation event evidence + entropy source declaration + key
identifier uniqueness checks
|
Jurisdiction-specific uniqueness assurance methodology |
[EU-ANNEX-II],
[ANDROID-KEYSTORE],
[WEBCRYPTO-L2]
|
| ANNEXII-1c |
Non-derivability and forgery resistance |
Algorithm policy + RNG quality + anti-rollback + verified
execution state
|
Policy bundle + provenance records + attestation claims |
Conformity-assessment acceptance gate |
[EU-ANNEX-II],
[RFC7515],
[RFC9052],
[ANDROID-AVB]
|
| ANNEXII-1d |
[=sole control=] by signatory |
Bound [=user intent ceremony=] + policy-enforced user
authentication
|
Intent log + auth policy evidence |
Legal identity attribution workflows |
[EU-ANNEX-II],
[ANDROID-PROTECTED-CONFIRMATION], [WEBAUTHN-L3]
|
| ANNEXII-2 |
No silent alteration and no blocked presentation prior to signing
|
Payload-hash binding + trusted confirmation path + verifier-side
integrity checks
|
Verification transcript + confirmation token + log inclusion proof
|
Local legal validation overlays |
[EU-ANNEX-II],
[RFC7515],
[RFC9052],
[ANDROID-PROTECTED-CONFIRMATION]
|